Using your email address as your username has become the standard. In many cases, you simply enter your email address and choose a password. Some services remove the need for a password altogether, allowing you to register using just your email address and a onetime code sent to it. Others offer the option to connect your account directly to your Google or Apple identity.
As we scroll, shop, apply, and register across services, our email address quietly becomes our identity everywhere, from shopping platforms to banking to travel. Over time, more and more of our activity starts pointing back to a single account.
While it all feels convenient, there is an issue we often forget. Our email is not just an access point. It holds sensitive information about us—both in what we receive and what we send—and it is tied to many, if not most, of the services we use.
We rely on it to receive one-time codes, confirm actions, and reset passwords. It is also where we communicate with accountants, bankers, doctors, and other providers, as well as for personal communication.
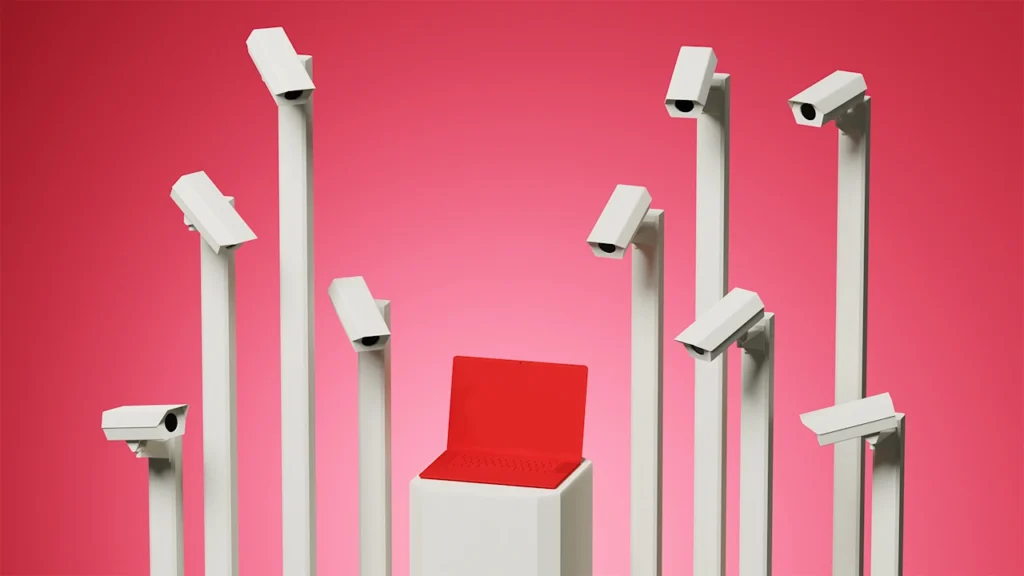
Over time, this turns our email into more than just another account. It becomes a central point of access, connected to multiple parts of our lives.
Your email is your identity
Every time you use your email to log into a service, you are connecting another account directly to it. Over time, more and more services become tied to that same identity, and your email becomes the place that links them all.
As a result, one email account ends up controlling access to many different accounts, across services that have nothing to do with each other.
If someone gains access to your email, they can use standard flows, password resets, login confirmations, and verification emails to access those connected services.
In addition, they gain access to a large amount of personal information, including medical records, financial details, addresses, contacts, and private communication. A targeted search can reveal patterns, surface sensitive data, and even help identify potential passwords or build more effective attack paths.
The threat of a compromised email is real
Recently, someone reached out to us after being contacted by their credit card company about a fraudulent charge. As cybersecurity consultants, we often assist in investigating a wide range of cyber incidents.
This is not unusual. Credit card fraud happens all the time, whether the card is stolen physically or the details are exposed online.
What stood out in this case was where the charge came from.
The transaction was tied to a town they had lived in about a year earlier, for a high-value concert ticket purchased through a website they did not recognize at first. After looking into it, they realized they had used that site once before and had forgotten about it.
We eventually discovered that they had logged in there previously using their email and a one-time code, which is a very common practice. There is no password to remember, no account to manage, just a quick login that leads directly to a purchase.
Once we connected the activity to that login method, the focus shifted to their email. If someone could access their email—whether through a compromised password or by bypassing it using standard recovery flows—they could request a login code and enter the account without needing anything else. We asked if their email account had multifactor authentication enabled, but they were not familiar with the concept. At that point, the concern was no longer just the credit card.
Their email contained years of information, previous addresses, financial details, services they had used, and ongoing communication. It was enough to map out their activity and identify additional targets.
It is also very likely that their email address had appeared in past data breaches. This is common, and it allows attackers to connect an email address to multiple services and focus their efforts.
Follow these best practices to keep your accounts safe.
Use multifactor authentication
Cybersecurity practitioners cannot emphasize enough the importance of multifactor authentication (MFA). This applies first to your email account, but it should not stop there. Any account you rely on, especially those tied to financial, personal, or sensitive information, should have it enabled.
Many people hesitate to enable MFA because they do not want to tie their phone number to their account. That is a valid concern.
The recommended approach is to use an authenticator app such as Google Authenticator, Microsoft Authenticator, or similar apps. It generates one-time codes on your device and does not rely on your phone number. While the setup may feel unfamiliar at first, it is a one-time process, and there are many simple guides that walk through it step by step. A simple search like “how to set up an authenticator app” will walk you through the process and explain the logic behind it. Do it once, and it becomes easy to apply everywhere else.
Use multiple email accounts
Using the same email everywhere flattens everything into one identity, even though the services you use are not all the same. Some services carry real weight, others are less clear, and some are simply disposable.
The best practice is to use different email accounts based on sensitivity, creating your own system of which email you use depending on the service.
Regardless of how you choose to structure it, you should enable multifactor authentication across all accounts.
Be intentional with one-click logins
Options like “Continue with Google” or “Continue with Apple” allow you to connect your identity instantly and skip creating an account altogether. While convenient, they should not be the default for every service.
When you use these options, you’re not just logging in. You’re granting the service access to parts of your account. That can include your name, email address, profile photo, and sometimes your contacts or other profile details. Do not skip the permission screen; take a moment to review what information is being requested before approving the connection.
If you run a business, consider doing this
For business owners, I strongly advise training employees not to use their corporate accounts for anything that is not related to their job. We have seen many cases where corporate email addresses appear in popular breached databases. Employees tend to use them for personal services, which can put additional attention on your corporate domain as a target.
Use a password manager
A password manager is a tool that stores and generates passwords for your accounts. Using one helps simplify the registration process. You don’t need to come up with unique passwords or remember them, while still following best practices of using a different, strong password for each account.
Most password managers work the same way. You create one strong master password, and the tool stores the rest for you. When you log into a website, it can automatically fill in your credentials, or suggest a new strong password when creating an account. Apple’s built-in Passwords app is one example that many users are already familiar with, alongside other commonly used password managers.
Setting it up is straightforward: Choose a reputable password manager, install it on your browser and phone, and create your master password. From there, start saving your existing logins and updating weak or reused passwords as you go.
Like any tool, it takes a short adjustment period, but once in place, it removes the need to remember passwords, and significantly improves your overall security. You might even end up loving it.
For business owners: There are corporate plans that allow you to manage and enforce proper password practices across your teams. This is a practical way to train employees to use passwords in a secure manner and reduce risk to your business.
Be careful with what you send over email
Email is often used to send sensitive information, documents, financial details, identification, or personal data, without much thought. This creates significant risk on multiple levels.
The risk is not only on your side. Once you send something, you lose control over it. If your account or the recipient’s account is compromised, that information is exposed.
When sensitive information is involved, avoid sending it in plain text or as a regular attachment.
Instead, use a secure link provided by the organization, such as a portal for medical, financial, or other sensitive documents, or ask how they prefer to receive encrypted files.
If that option is not offered, it is worth asking for it.
Your email is likely one of your most valuable assets. Treat it with the level of protection it requires.
—By Reut Hackmon, founder, Guidance Group
This article originally appeared on Fast Company’s sister website, Inc.com.
Inc. is the voice of the American entrepreneur. We inspire, inform, and document the most fascinating people in business: the risk-takers, the innovators, and the ultra-driven go-getters that represent the most dynamic force in the American economy.